Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks, Second Edition Book - EVERYONE - Skillsoft

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484204580: Amazon.com: Books
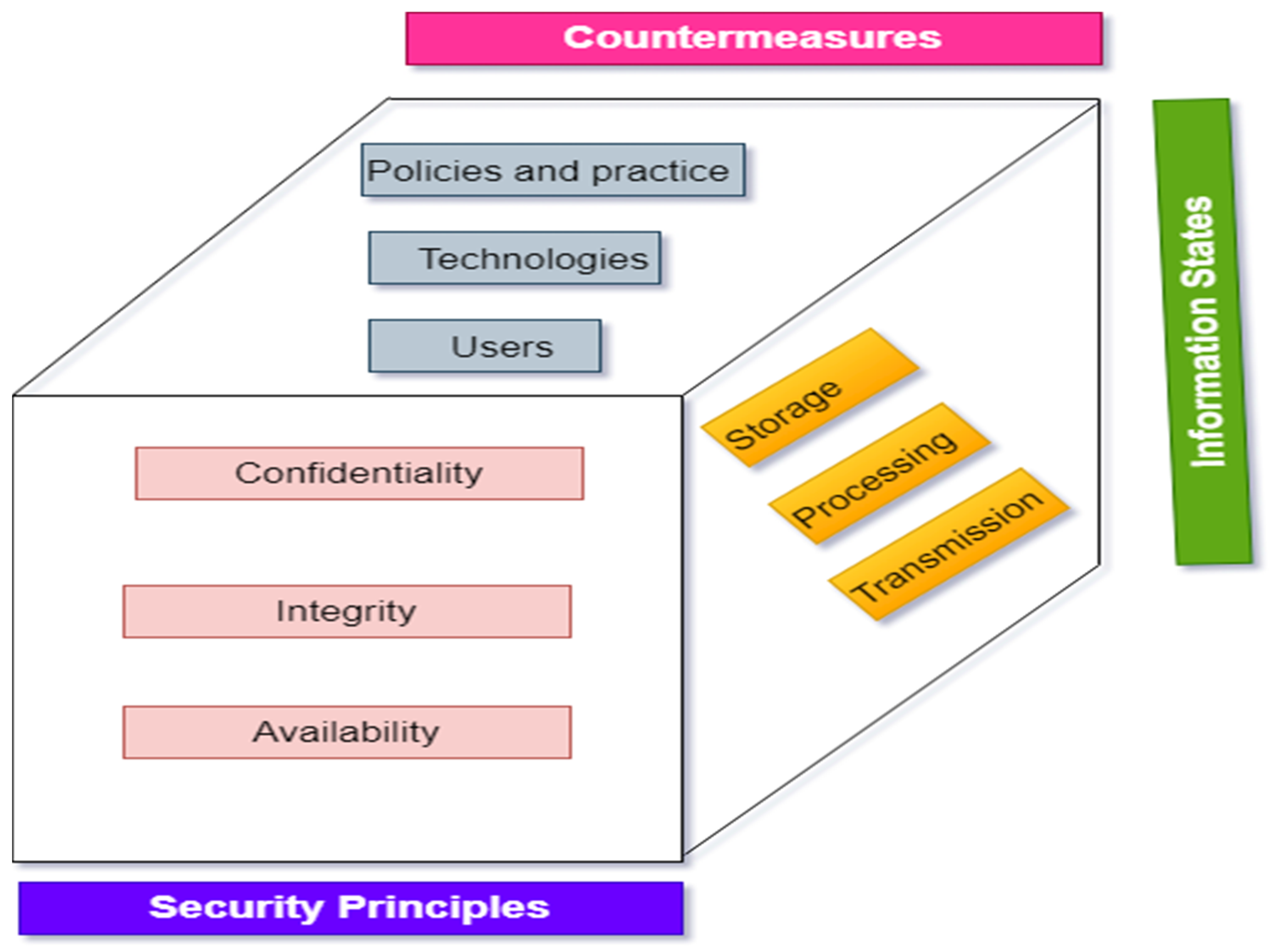
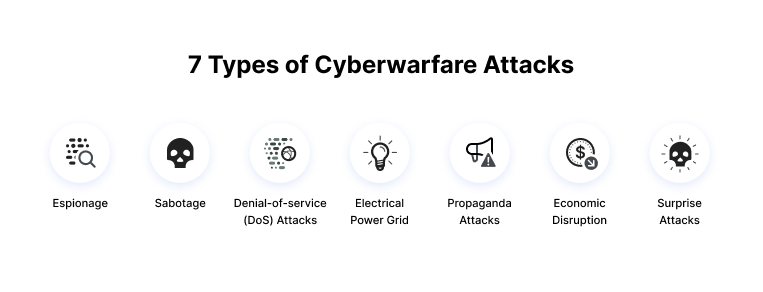
Electronics | Free Full-Text | A Comprehensive Review of Cyber Security Vulnerabilities, Threats, Attacks, and Solutions
![About the Author - Cyber Operations: Building, Defending, and Attacking Modern Computer Networks [Book] About the Author - Cyber Operations: Building, Defending, and Attacking Modern Computer Networks [Book]](https://www.oreilly.com/api/v2/epubs/9781484204573/files/images/9781484204580_unFM-01.jpg)
About the Author - Cyber Operations: Building, Defending, and Attacking Modern Computer Networks [Book]

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books
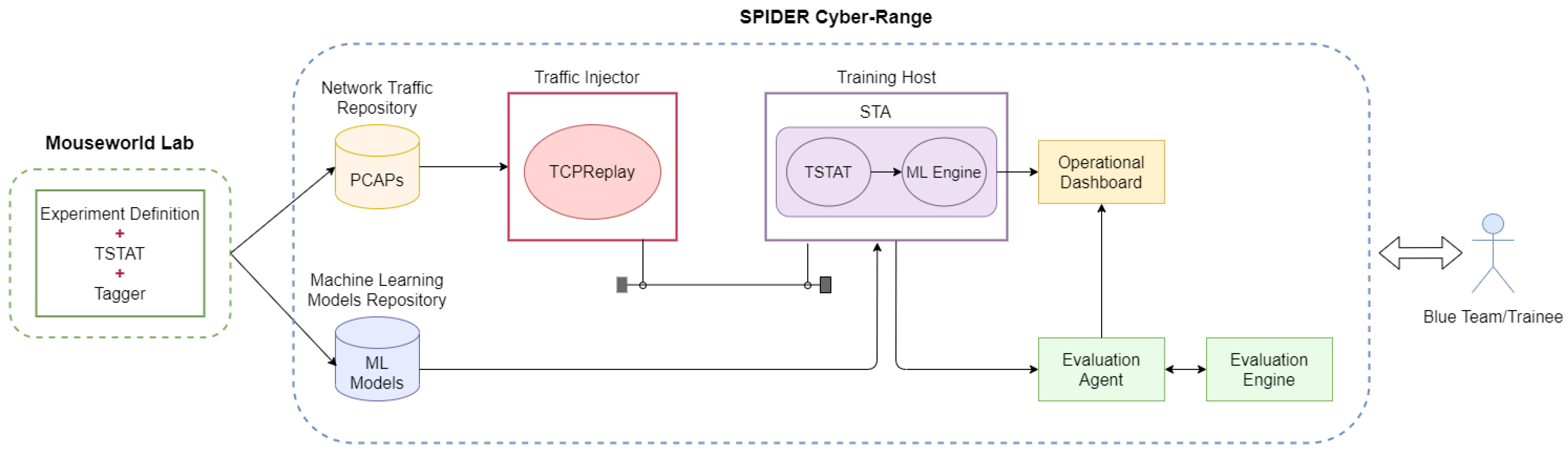
Applied Sciences | Free Full-Text | Integration of Machine Learning-Based Attack Detectors into Defensive Exercises of a 5G Cyber Range

Offensive Shifts, Offensive Policies: Cybersecurity Trends in the Government-Private Sector Relationship - Canadian Global Affairs Institute

Cyber attacks are rewriting the 'rules' of modern warfare – and we aren't prepared for the consequences

Defending the Expanding Attack Surface: Trend Micro 2022 Midyear Cybersecurity Report - Security Roundup